ressources · Governance & compliance
Law 25: what leadership actually needs to understand
Law 25 doesn’t just ask you to “protect data”. It requires you to demonstrate who has access, how long personal information is retained, and how incidents are detected and reported. This article gives you a leadership-ready version for an executive committee, without technical jargon.
Last updated: November 1, 2025 · AspharTech Solutions · Scope: Quebec / organizations with Quebec-based customers

1. What Law 25 concretely changes
Law 25 updates Quebec’s Act respecting the protection of personal information. It introduces the notion of a person in charge of the protection of personal information (RPRP), obligations for logging, registers and, above all, incident notification. Leadership needs to understand that responsibility is shared: Legal cannot do everything if the systems do not allow you to identify access or data transfers.
For an executive committee, the key message is simple: Law 25 compliance is not a one-off document to sign. It's the ability to demonstrate, at any time, that personal data is under control.
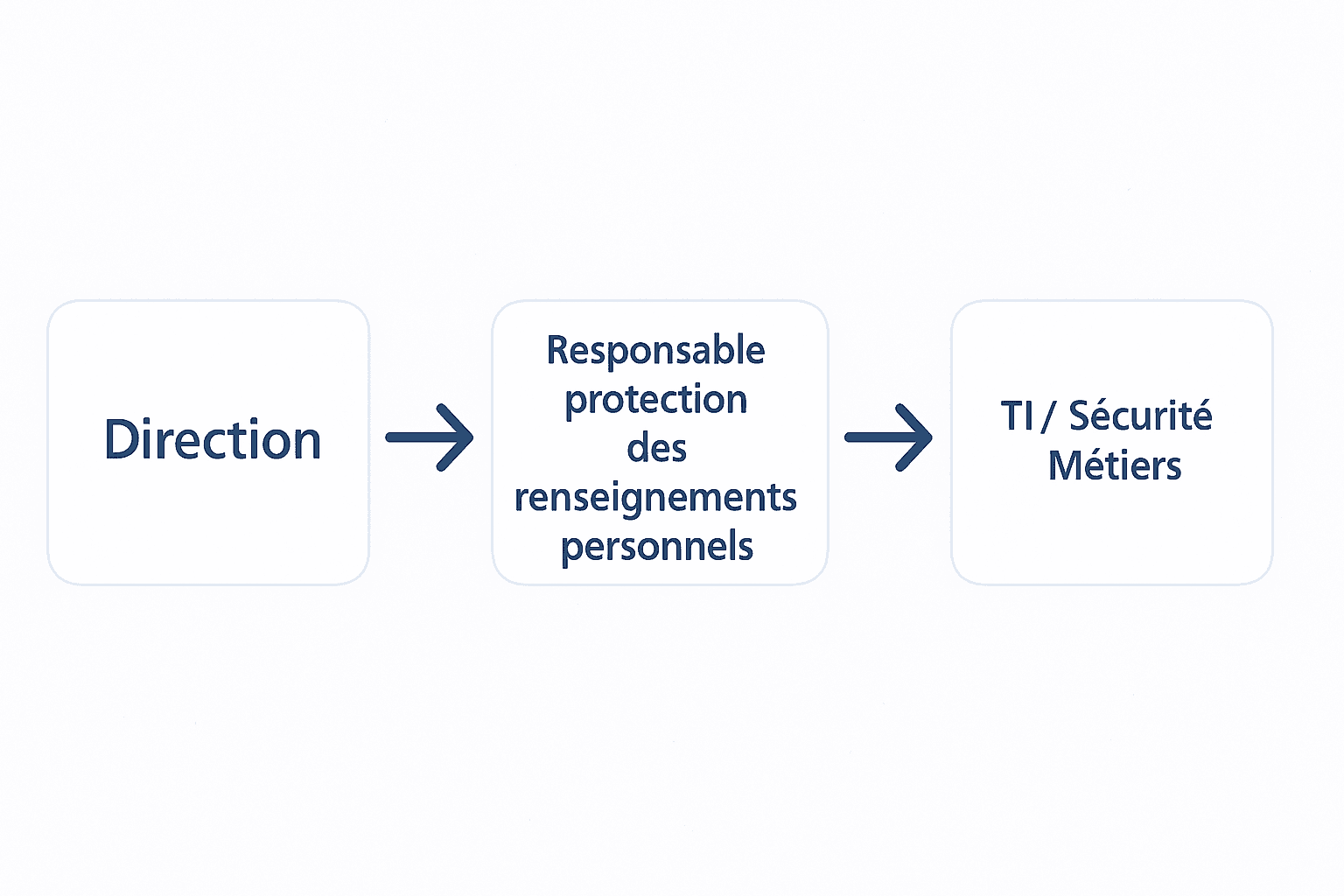
Example target setup: leadership defines acceptable exposure, the RPRP coordinates, IT/Security operates.
2. What leadership should validate first
Instead of receiving a very technical report, leadership needs a readable table. The model below can be re-used as-is in an executive committee.
This table is intentionally high-level: it's used to frame the discussion with leadership before diving into technical detail.
3. Role of the person in charge of personal information (RPRP)
A clearly identified role, not necessarily a full-time position.
Law 25 requires that a person be clearly identified. In an SMB, this is often the CEO or an IT leader. In a more structured organization, it can be a role reporting to leadership or Legal.
- Maintain the register of personal information
- Receive incident reports involving personal data
- Coordinate technical measures with IT / Security
- Act as point of contact if the CAI requests clarifications
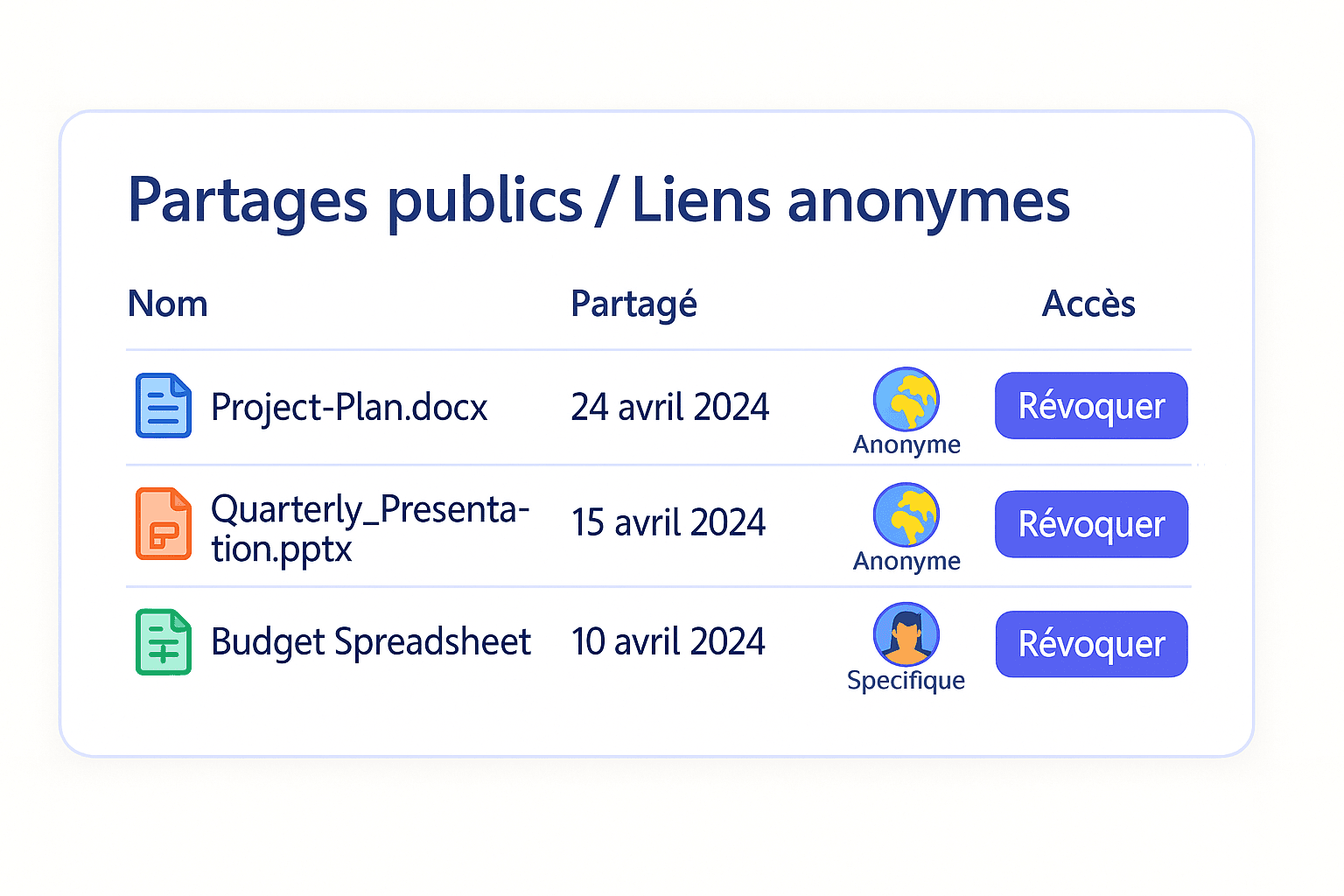
4. Risk areas to put on leadership’s radar now
These are often the issues leadership has never seen formally raised.
Some risks are purely operational but have a direct Law 25 impact. They should appear in a short memo to the executive team.
- • SharePoint / OneDrive spaces shared too broadly (exposure risk).
- • SaaS tools purchased by business teams with no validation or DPA.
- • Insufficient logging: impossible to reconstruct an incident.
- • Personal data sent by email without encryption.
5. How to present all this in a simple way
Leadership does not need a full course on Law 25. They need to know: what is mandatory, what is exposed today, what can be done quickly, and what will require budget.
A format that works well: 1 page “obligations”, 1 page “main gaps”, 1 page “90-day plan”. Everything else (detailed register, logs, DLP rules) stays within IT and Security teams.
For many organizations, applying good practices in Microsoft 365 / Google Workspace already covers a significant part of Law 25 expectations—as long as it is documented.
