Practical guide · Customer relationships
Preparing for a customer security audit without starting from scratch
When a strategic customer asks for security evidence, you need to respond quickly and cleanly without kicking off a 3-month project. This guide proposes a simple way to gather the right evidence, explain your context and strengthen the commercial relationship.
Last updated: November 2, 2025 · AspharTech Solutions
Why do these audits always seem to land at the worst time?
The scenario is classic: your customer wants to renew the contract, but their security team suddenly asks for a questionnaire, a register, backup evidence, and sometimes even your internal policies. Your IT team doesn’t necessarily have a SOC, or a full GRC in place, and yet you’re asked to respond within 5 to 10 days.
The right approach is not to rewrite everything, but to present your real level of security in a structured way – without creating inconsistencies between documents.
1. What the customer is actually trying to verify
Behind a vendor audit, there is rarely a desire to “catch you out”. The customer mainly wants to confirm that:
- • the data they entrust to you is identified and protected;
- • an incident on your side will not impact their own end customer;
- • you have a minimum level of traceability (logs, access, backups);
- • your team knows what to do if an account is compromised.
In other words: they want visibility and predictability. If you can show that your processes are alive (even if they’re simple), that’s often enough.
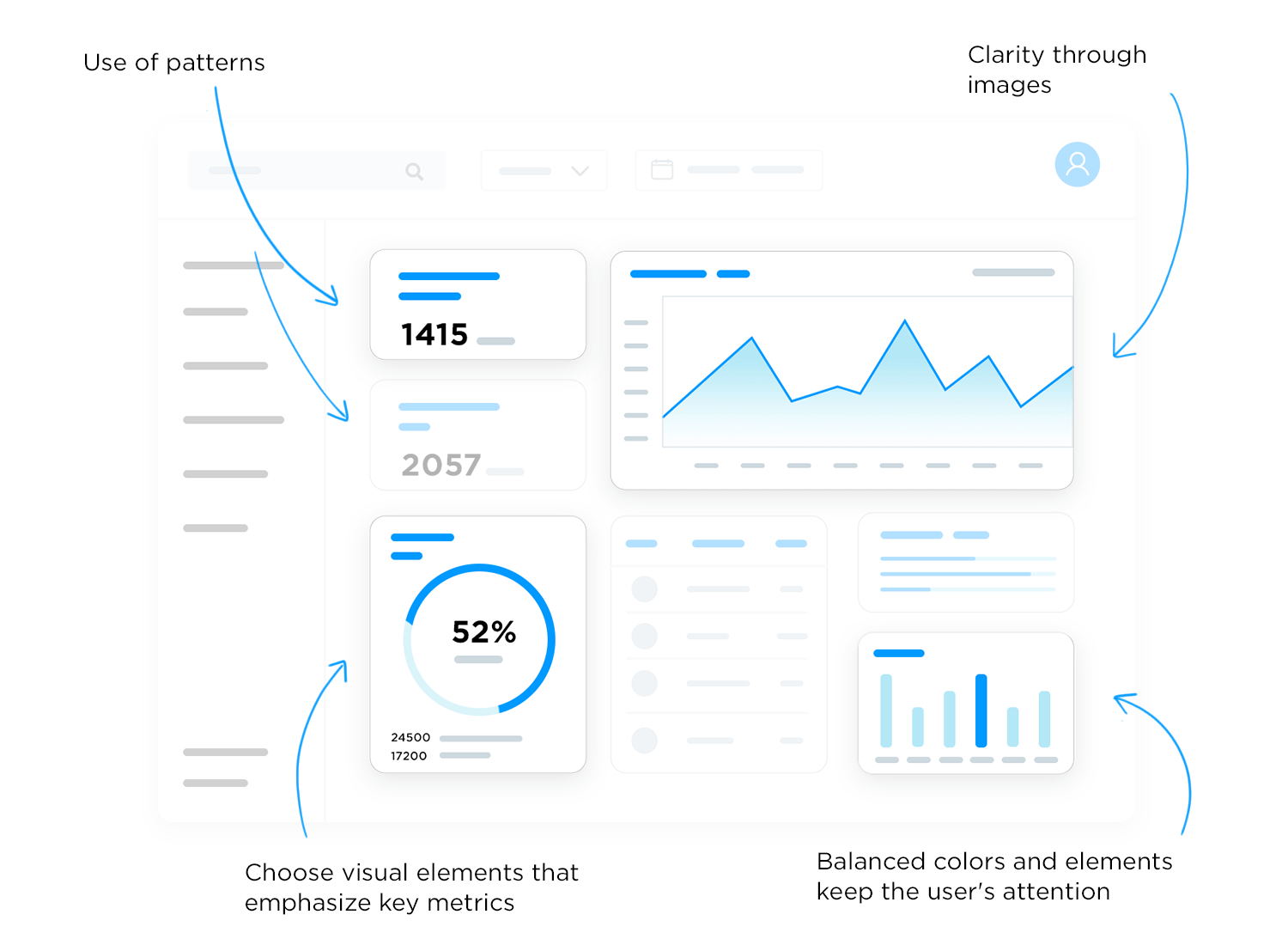
Example of an evidence tracking table: document, owner, last update date, status (sent / in progress).
2. Six pieces of evidence you should be able to send within 48 hours
To avoid wasting time, it’s useful to have a base set of “ready-to-send” evidence. Not necessarily perfect, but consistent.
1. Security policy or short memo
Even if it’s only 2 pages, it shows that security is framed and owned.
2. Description of access and MFA
Who can access the environment, how leavers are handled, and whether MFA is generalized.
3. Backup and recovery overview
Frequency, location, and evidence of recent restore tests.
4. Minimum logging
M365 or VPN activity, retention duration.
5. Account management process
Creation, modification and deprovisioning (HR, contractors, guests).
6. Register or list of IT vendors
To show that third parties are identified (Loi 25 / GDPR / privacy requirements).
3. Three common mistakes to avoid
- Sending contradictory documents. For example: one document says “MFA for everyone” but your logs clearly show otherwise.
- Promising full compliance overnight. The customer audit team wants to see a realistic plan, not a vague, oversized program.
- Leaving personal data unexplained. Clearly state how the customer’s data is processed, protected and deleted.
Conclusion
A well-managed customer audit strengthens the relationship, instead of weakening it. The key is to show that security is organised, even if everything isn’t industrialized yet. The next step can be to automate the collection of some evidence (M365 access, guests, backups) so you can respond faster.
This model can be reused for other customers, by only adjusting the level of detail.
